Over 14 million mobile malware attacks were blocked in 2025, with 255,000 banking trojans targeting Android identified that year alone. The Necro trojan slipped past Google’s defenses and hit 10 million phones through the Play Store. SpyLoan apps racked up 8 million installs before anyone caught on, stealing contacts, photos, and SMS messages for blackmail. If your phone is acting strange, there is a real chance something malicious is running on it.
You can remove malware from Android without being a tech expert. Most infections clear up without a factory reset if you follow the right sequence.
Fake virus popups, grayed-out uninstall buttons, apps that seem impossible to delete. These are the roadblocks that trip people up. We will walk you through 8 steps, from confirming an actual infection to locking down your accounts afterward.
Your first move is figuring out whether your symptoms point to real malware or a false alarm. The difference matters, because acting on a fake warning can actually install the threat you were worried about. Every step below works on Android 10 through Android 15, regardless of manufacturer.
Step 1: Confirm Your Android Phone Is Actually Infected
That scary popup saying “YOUR PHONE IS INFECTED” is almost certainly fake. Browser-based virus warnings are a scare tactic designed to trick you into downloading the actual malware. Close the browser tab and move on.
Real malware behaves differently. These are the symptoms that point to an actual infection:
- Pop-up ads appearing outside your browser, on your home screen or over other apps
- Apps you never installed showing up in your app drawer
- Sudden spikes in data usage with no change in your habits
- Battery draining abnormally fast or your phone overheating while idle
- Contacts reporting spam messages sent from your number
- Sluggish performance that started suddenly, not gradually
Some malware looks completely legitimate. The Necro trojan hid inside Wuta Camera and Max Browser, two apps that appeared normal. SpyLoan apps disguised themselves as loan calculators. Banking trojans tripled in 2024, reaching 1.24 million attacks, and most mimicked real banking or utility apps.
One more check: go to Settings > Battery and look for apps consuming unusual power in the background. Crypto-mining malware and spyware run constantly and show up here even when they hide from the app drawer.
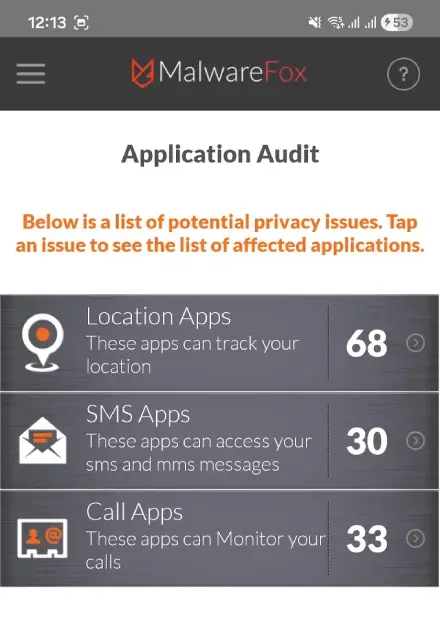
Additionally, you can use the Application Audit feature of MalwareFox app which gives the list of apps according to their permissions. So, if you find out ‘Calculator’ app requiring ‘Location’ permission, it is a red flag.
If you spot at least one symptom from the list above, move to the next step. If everything checks out, your phone is likely clean.
Step 2: Disconnect From the Internet and Switch to Safe Mode
Cut your phone off from the internet before you touch anything else. This stops malware from sending your data to an attacker’s server and prevents remote commands from triggering.
Enable Airplane Mode: Swipe down from the top of your screen and tap the Airplane Mode icon. You can also find it under Settings > Network & internet > Airplane Mode. Banking trojans exfiltrate login credentials in real time, and SpyLoan malware actively uploads your contacts and photos. Airplane Mode shuts that down immediately.
Boot into Safe Mode: Safe Mode disables every third-party app on your phone, including malware.
- Press and hold the Power button until the power menu appears.
- Long-press the “Power off” option.
- Tap “Safe Mode” when prompted.
Your phone will restart with “Safe mode” in the bottom-left corner. If your symptoms (pop-ups, strange behavior, overheating) disappear in Safe Mode, a third-party app is the culprit. That confirmation tells you the problem is removable without a factory reset.
Samsung users: The process is the same, but on some Galaxy models you need to press and hold Volume Down during restart instead. If the long-press method does not work, restart your phone and hold Volume Down as the Samsung logo appears.
Stay in Safe Mode for the next several steps. You will remove the malware while it cannot run or defend itself.
Step 3: Run a Google Play Protect Scan
Every Android phone with Google Play Services has a built-in malware scanner that runs automatically. Most people have never manually triggered it, which means it may not have scanned recently or thoroughly.
Google Play Protect scans 200 billion apps daily and blocked 13 million malicious apps outside the Play Store in 2024. It catches known threats fast, making it a strong first pass. Run a manual scan:
- Open the Google Play Store app.
- Tap your profile icon in the top-right corner.
- Select Play Protect.
- Tap Scan.
You may need to briefly disable Airplane Mode if Play Protect needs updated definitions. Re-enable Airplane Mode as soon as the scan finishes.
If Play Protect flags any apps, tap Uninstall to remove them immediately. If it comes back clean, do not assume you are safe. Play Protect is less effective against sideloaded APKs, newer zero-day threats, and malware that hides inside system processes. Think of this as the first layer of removal, not the last.
Also verify Play Protect is fully enabled. Tap the gear icon in the Play Protect screen and confirm both “Scan apps with Play Protect” and “Improve harmful app detection” are toggled on. Some malware silently disables these settings to avoid detection.
Step 4: Uninstall Suspicious Apps and Revoke Hidden Permissions
This is where most people get stuck. You find the malicious app, tap Uninstall, and the button is grayed out. The app has protected itself, but you can strip those protections manually.
Find the suspicious apps first. Go to Settings > Apps > See all apps. Look for apps with generic names (like “System Service,” “Update Manager,” or “Phone Cleaner”), missing icons, or install dates that line up with when your symptoms started. Also check for apps with unusually large storage usage relative to their stated purpose. Sort by date installed to surface recent additions quickly.
Try the standard uninstall. Tap the app, then tap Uninstall. If the button is grayed out, the app has granted itself Device Administrator privileges. Fix it:
- Go to Settings > Security > Device admin apps.
- Find the suspicious app in the list.
- Toggle it off and confirm.
- Go back to Settings > Apps, find the app, and tap Uninstall. It should work now.
Check Accessibility Services too. Go to Settings > Accessibility > Installed services. Malware abuses Accessibility permissions to read your screen, log keystrokes, and overlay fake login pages on top of real banking apps. Revoke access for anything you do not recognize.
Force stop before uninstalling. Some malware actively blocks its own removal while running. Tap Force Stop on the app’s info page before attempting the uninstall. This is especially important for adware that spawns overlay windows to prevent you from reaching the Uninstall button.
If the app still resists after revoking both Device Admin and Accessibility permissions, remove the Hidden Device Administrator. It finds malware that hides from the standard Device Admin menu. For anything truly stubborn, MalwareFox in the next step can handle it.
Step 5: Scan With MalwareFox to Catch What You Missed
Manual removal catches visible threats. Trojans hiding in system processes, residual files left behind by deleted apps, and rootkits need a dedicated scanner to remove malware from Android completely.
Play Protect focuses on apps distributed through the Play Store. Sideloaded APKs, browser-injected adware, and deeply embedded trojans often slip past it. A common scenario: a device’s primary scanner misses multiple trojans that a second, specialized scanner catches on the same phone. Layered scanning closes that gap.
Run a full scan with MalwareFox:
- Briefly disable Airplane Mode to access the internet.
- Download MalwareFox Antimalware from the Google Play Store.
- Open MalwareFox and update the threat definitions.
- Run a Full Scan.
- Re-enable Airplane Mode after the download and update are complete.
MalwareFox lists every detected threat with its type (adware, trojan, spyware, etc.). Remove all of them. Pay attention to the threat categories. If MalwareFox flags a banking trojan or spyware, treat the account lockdown in Step 8 as urgent, because those categories mean your credentials are likely compromised.
After the scan, exit Safe Mode by restarting your phone normally. Verify that the symptoms from Step 1 are gone. If pop-ups or strange behavior return, repeat Steps 4 and 5 before moving forward.
Keep MalwareFox installed after cleanup. Its real-time protection catches malicious apps before they can do damage. Recovery from a single malware attack averages 50 days, so prevention is far cheaper than cleanup.
Step 6: Clear Your Browser and Downloads Folder
Malware often leaves behind cached scripts, rogue notification permissions, and redirect chains in your browser even after the app itself is gone. These leftovers can re-trigger pop-ups or download new malware.
Reset Chrome to clean defaults:
- Go to Settings > Apps > Chrome.
- Tap Storage.
- Tap Clear cache, then Clear all data (or Manage Space > Clear All Data).
This wipes malicious redirects, injected bookmarks, rogue notification permissions, and cached scripts. Repeat for every browser on your phone: Firefox, Samsung Internet, Opera, or any other you use.
Clean the Downloads folder next. Open your Files app and navigate to Downloads. Delete any APK files, suspicious PDFs, or files you did not intentionally download. APK files are Android installation packages that may contain malware waiting to be opened. Sort by date to find files that arrived around the time your symptoms started.
Check notification permissions. Go to Settings > Notifications > App notifications and revoke notification access for any app you do not recognize. Malware frequently grants itself notification permissions to push fake alerts even after its main payload is removed.
Step 7: Factory Reset as a Last Resort (With the Google Backup Trap)
If malware persists after Steps 1 through 6, a factory reset is your next option. But there is a critical mistake most guides skip: restoring from Google Backup can silently reinstall the malware.
Back up only clean data first. Manually copy your photos, documents, and important files to a computer using a USB cable. Export your contacts through contacts.google.com in a browser. Do not rely on Google’s automatic backup for the restore, because it can bundle the malicious app right back onto your phone.
How to factory reset (stock Android):
- Go to Settings > System > Reset options.
- Tap Erase all data (factory reset).
- Follow the confirmation prompts.
On Samsung: Go to Settings > General Management > Reset > Factory Data Reset.
After the reset, this part is critical. When your phone restarts and shows the setup wizard, choose to set up as a new device. Do not tap “Restore from backup.” Install your apps fresh from the Play Store, one at a time. Before reinstalling each app, check its reviews and permissions to avoid reintroducing the same threat under a different name. Reinstall MalwareFox early and run a scan before loading sensitive apps like banking or email.
What a factory reset cannot fix: The xHelper malware infected 45,000+ devices and survived factory resets by modifying a core system file called libc.so. If your symptoms return after a clean factory reset with no backup restore, you are dealing with firmware-level malware. At that point, the device needs professional firmware reflashing or replacement.
Step 8: Lock Down Your Accounts and Prevent Reinfection
Removing malware from your phone is only half the job. If a trojan ran on your device for days or weeks, it may have already captured passwords, session tokens, and financial data.
Change your critical passwords immediately. Start with your Google account, then email, banking apps, and social media. Do this from a different device (a computer or someone else’s phone) if possible, since your Android may still have cached session tokens at risk. Use unique passwords for each account.
Revoke suspicious third-party access. Go to myaccount.google.com > Security > Third-party apps with account access. Remove anything you do not recognize or no longer use. Do the same for connected apps in Facebook, Instagram, and other platforms.
Check your financial accounts. Review bank and credit card statements for unauthorized transactions going back at least 30 days. Banking trojans tripled to 1.24 million attacks in 2024, making financial theft one of the most common outcomes. Enable transaction alerts so you catch unauthorized charges within minutes. If you find suspicious activity, contact your bank immediately and request a card replacement.
Prevention habits going forward:
- Only install apps from the Google Play Store
- Keep Google Play Protect enabled at all times
- Never grant Accessibility permissions to apps that do not genuinely need them
- Avoid sideloading APK files from websites or messaging apps
- Keep MalwareFox installed for real-time protection
- Enable two-factor authentication on your Google account and all critical services
A factory reset removes most malware by wiping apps, settings, and data. Advanced threats like xHelper can survive by embedding in system files. Restoring from Google Backup can also reintroduce malware. Always set up as a new device after resetting.
The app likely has Device Administrator privileges, which grays out the Uninstall button. Go to Settings > Security > Device admin apps, toggle off the suspicious app, then uninstall normally. Check Accessibility Services too.
Play Protect scans 200 billion apps daily and blocked 13 million malicious apps in 2024. It struggles with sideloaded APKs, zero-day threats, and malware in system processes. Pair it with a dedicated anti-malware app like MalwareFox for fuller coverage.
Yes. The Necro trojan reached 10 million devices through Play Store apps like Wuta Camera and Max Browser. SpyLoan apps hit 8 million installs before removal. Always check reviews, developer history, and requested permissions before installing.
Change all critical passwords from a clean device. Revoke suspicious third-party app access in your Google account settings. Review bank statements for unauthorized charges. Enable two-factor authentication and keep MalwareFox installed.
Thank you so much was super helpful. Very smart